How Does a Hash Help Secure Blockchain Technology in Real-Time Systems

Blockchain technology, which offers unparalleled security, transparency, and decentralization, has completely changed the digital landscape. However, if we dissect this seemingly impenetrable fortress, we find that the cryptographic hash function is the fundamental element that keeps it intact. Hashing plays an even more important role in real-time systems, where timing and data accuracy are vital.
Let’s explore the complex realm of hashing and discover how this mathematical wonder contributes to real-time blockchain security.
What Is a Hash and Why Does It Matter?
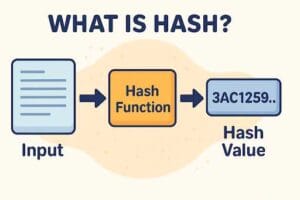
At its most basic, a hash is a fixed-length string of characters produced by a mathematical algorithm that transforms input data—regardless of its size—into a unique string. Since this transformation is one-way, data cannot be undone once it has been hashed. Strong security benefits are provided by this property alone. The true magic, though, occurs when hashes are employed within a blockchain.
A hash functions similarly to a fingerprint in real-time systems, where quick data validation and verification are crucial. The hash guarantees that the data hasn’t been altered, regardless of how long a transaction takes—a few hours or a few seconds. The key characteristics of hash functions are contrasted with more conventional security measures found in other data systems in the following breakdown:
| Feature | Hash Function (Blockchain) | Traditional Mechanisms |
| One-way Encryption | Yes | Sometimes |
| Tamper Detection | Immediate via hash mismatch | May require audit logs |
| Processing Speed | Fast and scalable | Slower in high-load scenarios |
| Collision Resistance | High (SHA-256 and beyond) | Lower (dependent on algorithm) |
| Data Integrity in Real-Time | Strong | Moderate to Weak |
Hashes, as you can see, are especially well-suited to satisfy the needs of real-time systems, especially those that need immediate trust and verification, like automated logistics, IoT networks, or financial transactions.
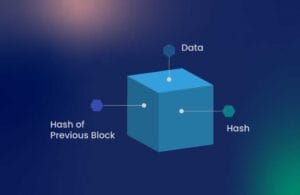
The Role of Hashing in Blockchain Architecture
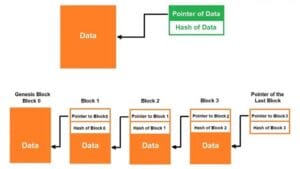
In essence, a blockchain is a series of blocks, each of which has a timestamp, data, and a cryptographic hash of the block before it. Because of the interconnected system this design creates, changing one block would render all subsequent blocks invalid. It’s all connected by the hash.
New data is hashed using algorithms like SHA-256 (Secure Hash Algorithm 256-bit) when it enters a blockchain. Together with the data, this output is stored, creating an unchangeable record. In order to create an interconnected “chain” that is naturally impenetrable, the block additionally contains the hash of the previous block.
In real-time systems, where security and latency must coexist, this structure is extremely helpful. Take a supply chain network, for example, where goods are continuously tracked across international checkpoints. Every modification
Why Is Hashing Perfect for Real-Time Environments?
Systems operating in real time are harsh. They depend on promptness, accuracy, and responsibility. Error and lag are not acceptable. These issues can be resolved with cryptographic hashing, which has the following clear benefits:
Instant Verification: By comparing hash outputs, any piece of data can be verified in a matter of milliseconds.
- Minimal Overhead: Because hashing requires little computing power, it can be used in high-frequency settings such as real-time monitoring or trading platforms.
- Immutable Logging: After data has been recorded and hashed, even a single bit change will result in a drastically different hash, making tampering easily identifiable.
Moreover, hashes only represent data in a safe, condensed format; they do not encrypt it. Because of this, they are quick and perfect for systems that prioritize data integrity over confidentiality alone.
How Do Hashes Prevent Fraud and Tampering in Blockchain?
A single block’s hash is changed when it is tampered with. This disparity propagates like a virus along the chain since each block contains the hash of the one before it. Without re-hashing each subsequent block, which is such a massive computational task that it discourages even the most determined attackers, fraud is all but impossible due to this cascading effect.
Hashes guarantee that every vote is recorded in an unchangeable state in real-time applications, like electronic voting systems. The hash mismatch instantly highlights any inconsistency if someone tries to add or remove votes after the fact.
Popular Hash Functions Used in Blockchain
Hashing functions are not all made equal. Some are more secure, while others are quicker. You will often come across the following in blockchain technology:
- SHA-256: Currently the gold standard for blockchain hashing, it is used in Bitcoin.
- Ethereum adopted Keccak (SHA-3), which is renowned for its adaptability and defense against different kinds of attacks.
- RIPEMD-160: Often used for address generation in cryptocurrency wallets.
Although each has advantages, they are all designed to withstand collision attacks, preserve high entropy, and produce deterministic results—essential characteristics for guaranteeing the integrity of real-time systems.
Blockchain + Hashing in Real-Time Applications

Let’s look at some actual systems where blockchain hashing is already causing a stir:
Healthcare: To avoid medication errors, prescriptions and real-time patient data are hashed and stored.
- Banking: Hash-based verification is used to approve transactions for instant fund transfers.
- IoT Networks: To avoid spoofing, devices authenticate and communicate using hashed identities.
- Smart Contracts: These ensure no human intervention by executing automatically in real-time based on hashed logic conditions.
By eliminating barriers to trust, reducing fraud, and significantly enhancing system responsiveness, these applications are transforming entire industries.
Limitations and Future Challenges
Despite its strength, hashing has drawbacks. For instance:
- Current hash algorithms** like SHA-256, which could eventually be cracked by qubits, are in danger of being disrupted by quantum computing.
- Even though they are uncommon with contemporary algorithms, hash collisions are still a possibility.
- If hash storage isn’t optimized, scalability may become a problem, especially in blockchains with a high transaction volume.
Future-proof solutions are already being paved by continuous research into adaptive hashing methods and post-quantum cryptography.
Final Thoughts
Hashing functions are the unseen guardians in the high-stakes realm of real-time systems and blockchain. They guarantee that every transaction is authentic, that no records are altered, and that every system is robust—even in the face of extreme strain. Hashing is at the core of the security architecture for decentralized systems today—and for the innovations of tomorrow—because it provides blazing-fast verification, immutable logging, and strong fraud resistance.
Q&A – Frequently Asked Questions
In the context of blockchain, what is a hash exactly?
A hash is a distinct string that is produced from data by a cryptographic algorithm. It contributes to the blockchain’s data security and integrity.
Q: In real-time systems, how does hashing identify tampering?
A: The hash of any piece of data changes significantly if it is even slightly changed. Tampering is immediately revealed by this disparity.
Which hash algorithm is used in blockchain technology the most often?
A: SHA-256 is the most widely used algorithm, especially in Bitcoin and other well-known cryptocurrencies.
Is it possible to recover the original data by reversing hashes?
A: Not at all. Hashes are intended to be irreversible and are one-way functions.
What makes hashing crucial in real-time settings like financial systems?
A: It offers immediate data validation, facilitating safe transactions with little waiting time.
What distinguishes encryption from hashing?
A: While encryption jumbles data that can be decrypted with a key, hashing produces a fixed representation of data that cannot be undone.
Are all hashing algorithms safe?
A: Not at all. There are known flaws in older algorithms like MD5 and SHA-1. SHA-256, Keccak, or even more sophisticated algorithms are used in modern systems.
Is it possible for quantum computers to crack hash functions?
A: Possibly. For this reason, quantum-resistant hashing methods are constantly being developed.




One Comment